# Insert key – was flashing green at first, flashing orange after software installed
# As root
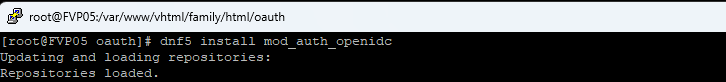
# Install required packages
sudo dnf install pam-u2f fido2-tools yubikey-manager pamu2fcfg
# As the user
# See note below re: setting pin
# The FIDO2 PIN must be at least 4 characters, and supports any type of alphanumeric characters. Some YubiKeys can be configured to require a longer PIN. (https://docs.yubico.com/software/yubikey/tools/ykman/FIDO_Commands.html)
ykman fido access change-pin
# List current fingerprints – should be none, since no user is set up, will prompt for your pin
ykman fido fingerprints list
# Add your fingerprint – RI stands for “right index” and is essentially a display name for the fingerprint (https://docs.yubico.com/software/yubikey/tools/ykman/FIDO_Commands.html#ykman-fido-fingerprints-add-options-name)
# Green light is fast flashing & prompted to touch sensor. Not a slide, touch and remove finger. It prompts with how many more scans are needed & reports when the print is not read (capture failed, recenter your finger and try again)
# Key stopped flashing
ykman fido fingerprints add RI
# Set up pam to use key/print as auth
mkdir ~/.config/Yubico
chmod 700 ~/.config/Yubico
# Run command, when key flashes green touch it with the registered finger
pamu2fcfg –username “$USER” –origin “pam://$(hostname)” >> ~/.config/Yubico/u2f_keys
chmod 600 ~/.config/Yubico/u2f_keys
# Back as root
authselect current
# Results:
Profile ID: local
with features:
with-silent-lasting
with-mdns4
with-fingerprint
# If nothing is selected, run the following and use “-b sssd” instead of “-b local” below.
# authselect select sssd
authselect create-profile yubikey -b local
authselect select custom/yubikey with-silent-lastlog with-mdns4 with-fingerprint
# Edit two files
/etc/authselect/custom/yubikey/system-auth
/etc/authselect/custom/yubikey/password-auth
# Add this line near the top of the auth section, before the usual pam_unix.so / pam_sss.so lines:
auth sufficient pam_u2f.so authfile=.config/Yubico/u2f_keys cue userverification=1
authselect apply-changes
# Test before rebooting and losing the currently logged on session
ctrl-al`-f3 and log into the alt console
Note: You may be prompted for the FIDO2 PIN in cases like:
You haven’t enrolled fingerprints (or user verification isn’t available), and the system/app requires verification.
Too many failed fingerprint attempts and the key requires a PIN to re-enable verification.
Certain management actions (adding/removing fingerprints, resetting FIDO2, etc.).
# If not working, update the custom system-auth and password-auth to debug output
auth sufficient pam_u2f.so authfile=%h/.config/Yubico/u2f_keys cue userverification=1 debug debug_file=/var/log/u2f.log
# Initialize file, otherwise debug output goes to screen
touch /var/log/u2f.log
On GUI logon, you have to hit enter (or the arrow) like you are logging in with a password (but you don’t have to type the password) and touch the thing when it flashes green
If you register new fingerprints on the key, you do not need to regenerate your keys file
KDEWallet will prompt to store every new fingerprint you use.