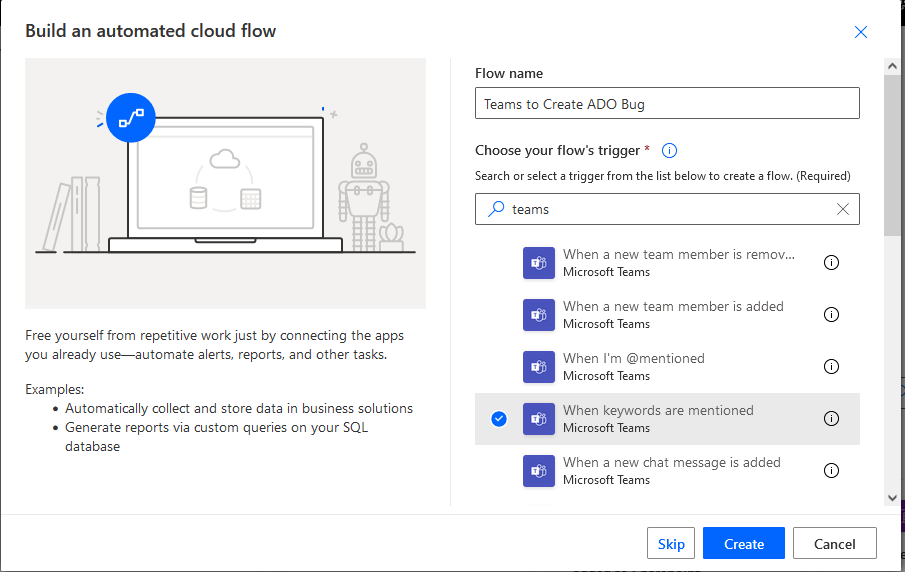
You can use Power Automate to create an ADO work item (bug, user story, etc) when a user posts into specific Teams channel.
Log into Power Automate and create a new workflow. Find a Teams trigger that suits your need – in my case, I wanted to use a key word (you could even use different key words to create work items in different projects or with different content). Note that automation cycles accrue based on execution — so if you elect to link up to a busy Teams channel and filter for keywords to indicate you want an ADO item created, you may be “wasting” workflow cycles. In our case, I have a “user group” Teams space and set up a special channel where users can submit bug and feature requests. This means workflow cycles are accrued when someone specifically wishes to create an ADO item not when messages are posted into the user group’s general chat channels.
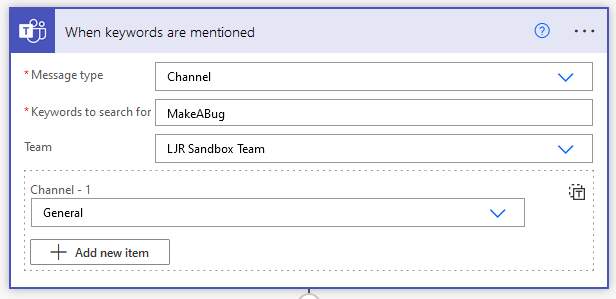
You can source messages from channels or group chats in the “Message type” selection. You cannot use hash-tags as key words! The workflow execution reports a gateway error. Select the Team and channel(s) that you want the workflow to monitor.
Add a new step to “create a work item” from Azure DevOps
Configure the project into which you want to create the work item – the organization and project name, the type of work item, and content of the work item.
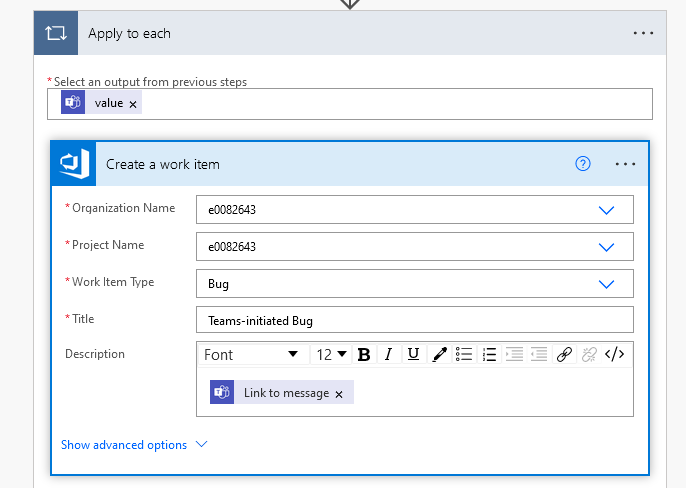
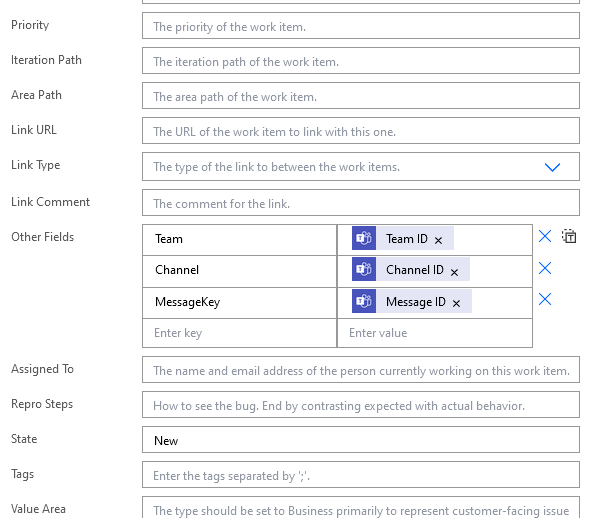
If you want to set priority, add an assignment, etc – click on “Show advanced options”. I added a few fields to provide a clue as to where the bug report came from.
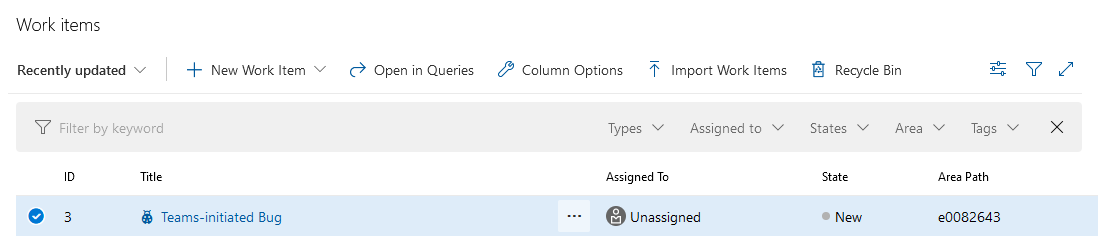
Save the workflow and post a message in your channel with the key word. Go into the ADO project work items; your Teams-initiated bug should be there.